Sensitive Activities (Layer 4)
Sensitive Activities are any type of action that might introduce risk to the organization, creating the need for governance. They are at the heart of the Gemara Model, and the entire reason GRC has existed in myriad forms throughout history.
Sensitive activities may take any number of forms: the building code regulating how a bank branch is built, the rules a teller needs to follow to stay within the law, the processes a development team must follow when creating a new mobile app, and the requirements placed on the software code itself.
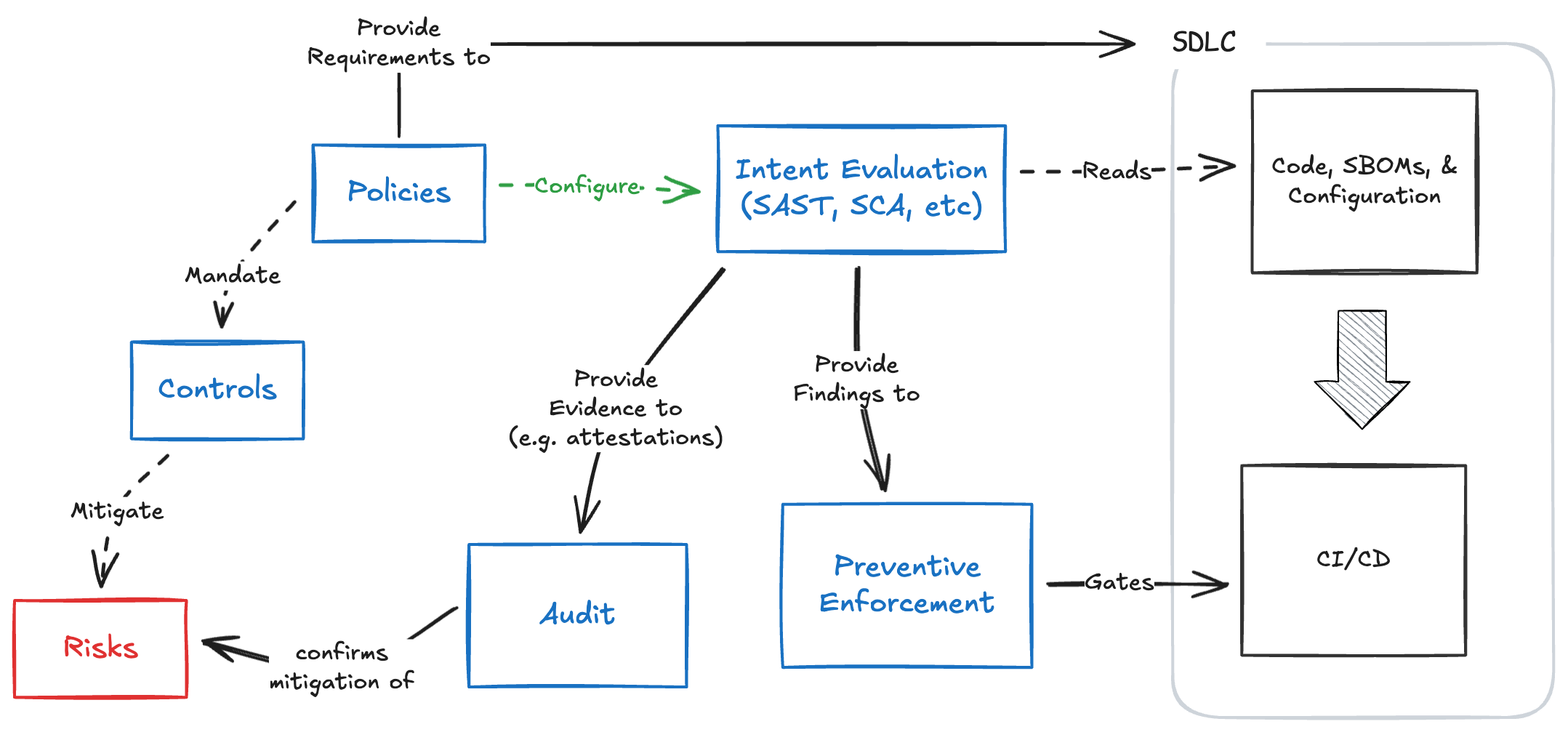
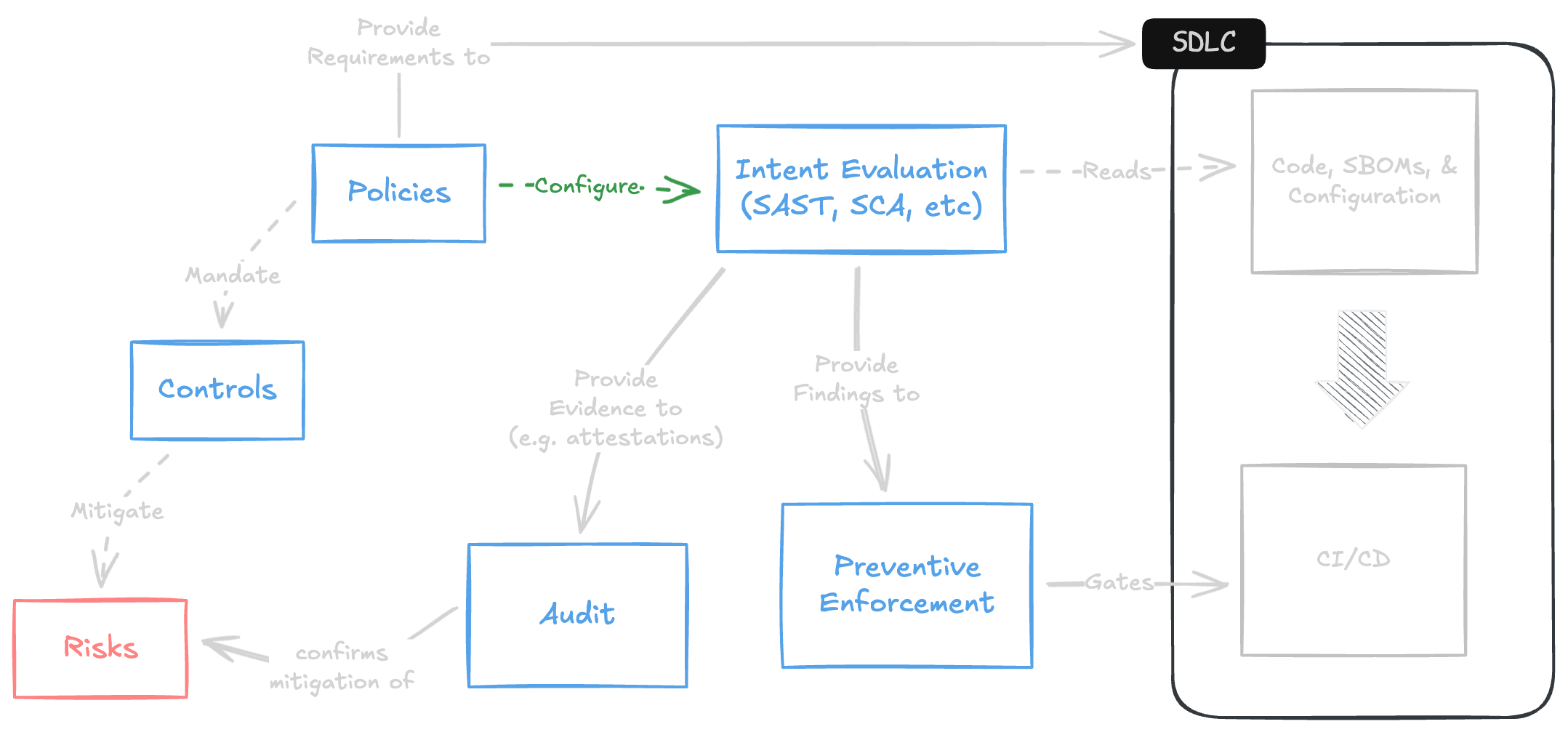
The model helps provide essential context to work that is already common. Figure 6.1 uses the model to help demonstrate the different categories of work that are necessary to ensure a stable and secure software supply chain. Policies are used to inform both development workflows and evaluation tools such as software composition analysis (SCA). For full maturity, the SCA findings should then be integrated into an enforcement mechanism as well as compliance audits. While some tools provide multiple elements of this process, leaders can reference the model to ensure that all the essential activities are being performed.
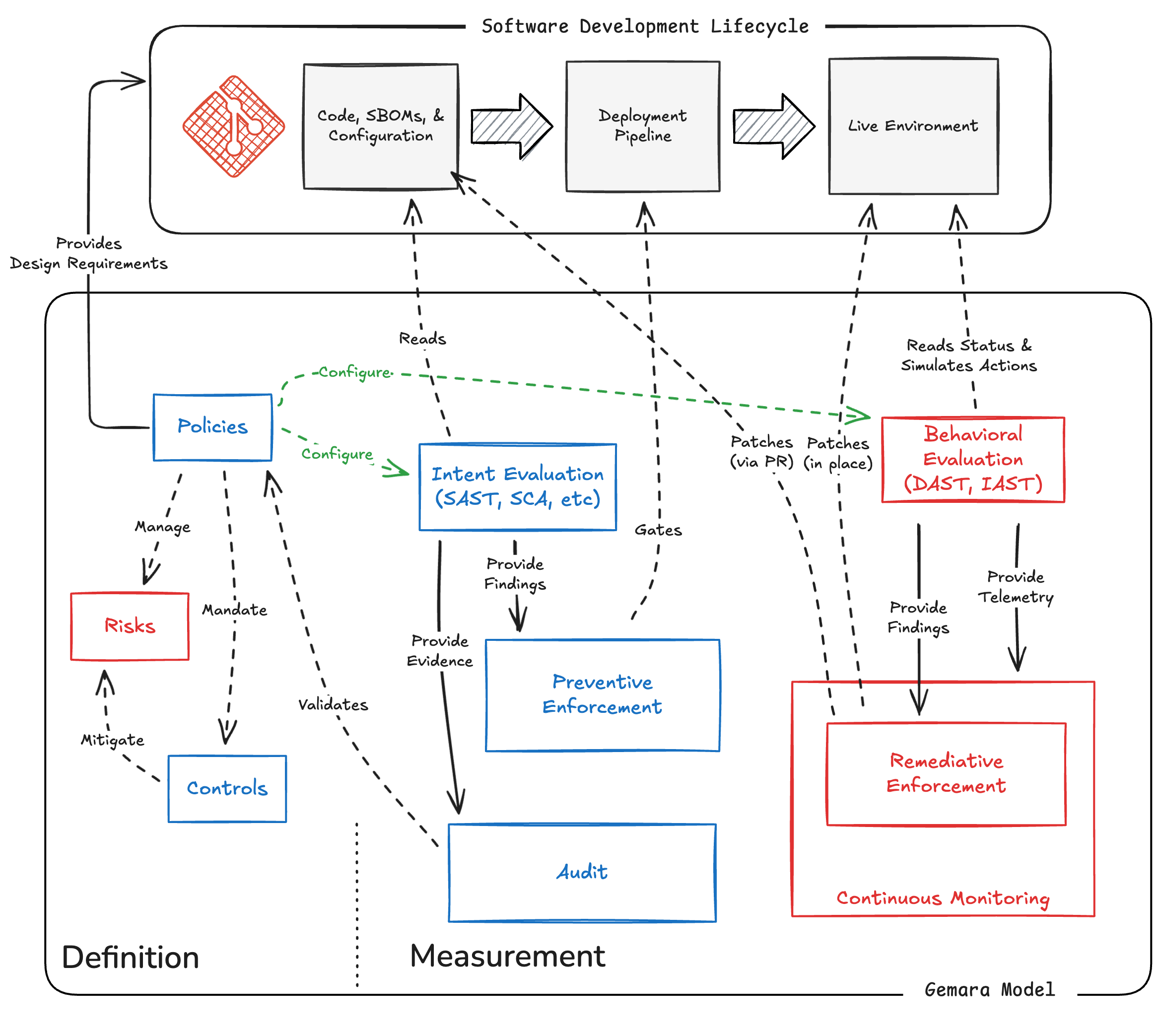
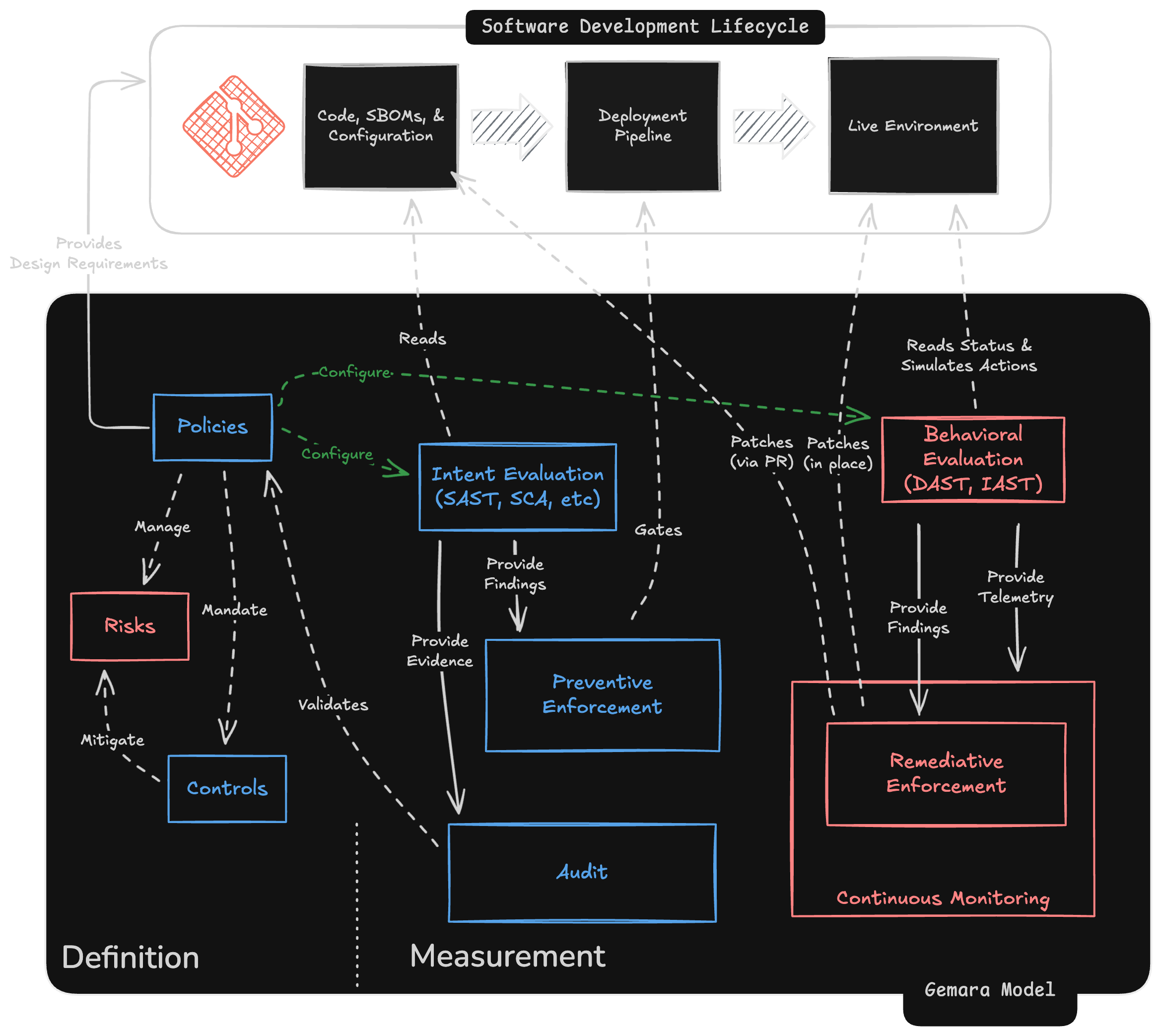
We see a fuller example in Figure 6.2, continuing the process into evaluation of live runtime environments. When fully integrated, findings operate as the last stage of the software development lifecycle — similar to quality assurance, user acceptance testing, and product feedback.
Continue Reading
- < Previous Page: Layer 3
- > Next Page: The Measurement Layers