Layer 3
Risk & Policy
The respective authority of any Control or Guidance is strictly dependent on when and how it is referenced by an organization. This is the phase where Risk Assessments exit the conceptual phase and meet reality. When done well, this ensures that Controls are appropriately selected based on the most relevant details.
Precisely defining Risk requires a firm understanding of an organization’s landscape: everything from technical to geopolitical details. It is typically informed by a Threat Assessment, to calculate the situational likelihood of a negative outcome, which is then compared to the impact it would have on the organization in the context of a particular Sensitive Activity. This may include elements such as the technologies used, the staff involved, and the value of the resources being handled.
Not all Risk is handled the same, however. Risk Appetite is the level of Risk an organization is willing to accept in pursuit of its objectives. Risk Appetite should be clearly represented in a Risk Catalog, which is used to determine when and how rules are created for the organization. A Policy is a clearly-scoped set of rules based on an organization’s Risk Appetite. It provides Governance rules that, while based on best practices and industry standards, are tailored to an organization. Because Policies inevitably introduce some level of Risk Acceptance, they cannot be properly developed without consideration for organization-specific Risk Appetite.
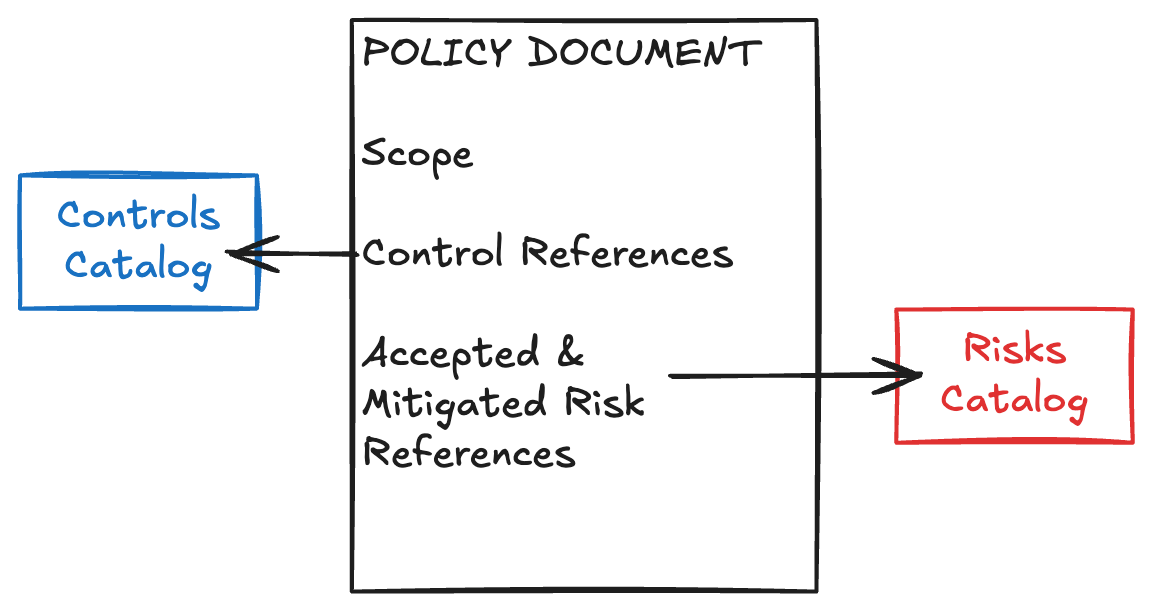
A complete Policy document will be time-bound, contain references to Threat-informed Controls with Assessment Requirements, and include a clear plan for rolling out the Policy to impacted parties.
Policy documents may be referenced by other Policy documents, creating a functional inheritance model. These documents can be distributed to relevant parties as design requirements and used as a starting point for Layer 5 Assessments. They are significantly more likely to succeed in practice when Risks are included with the distribution of a Policy, where they are mapped to specific Threats and subsequent Controls.
If created during planning, a Policy document can serve as a functional design requirement to ensure that security is baked into the sensitive activity instead of becoming an obstacle later.
Continue Reading
- < Previous Page: Layer 2
- > Next Page: Layer 4: Sensitive Activities